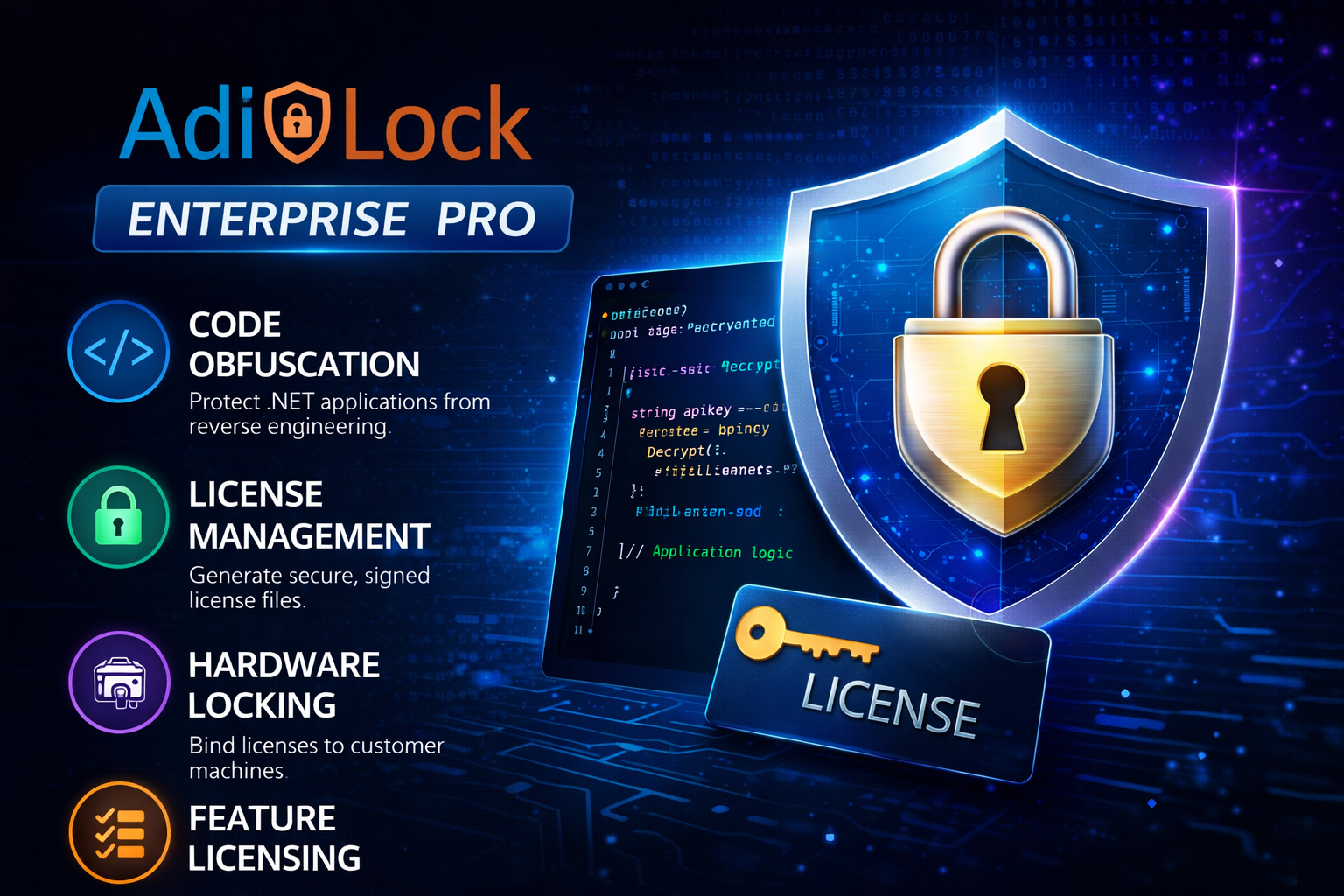
Enterprise Pro Edition
Advanced .NET Obfuscation & Licensing Solution for Secure Applications
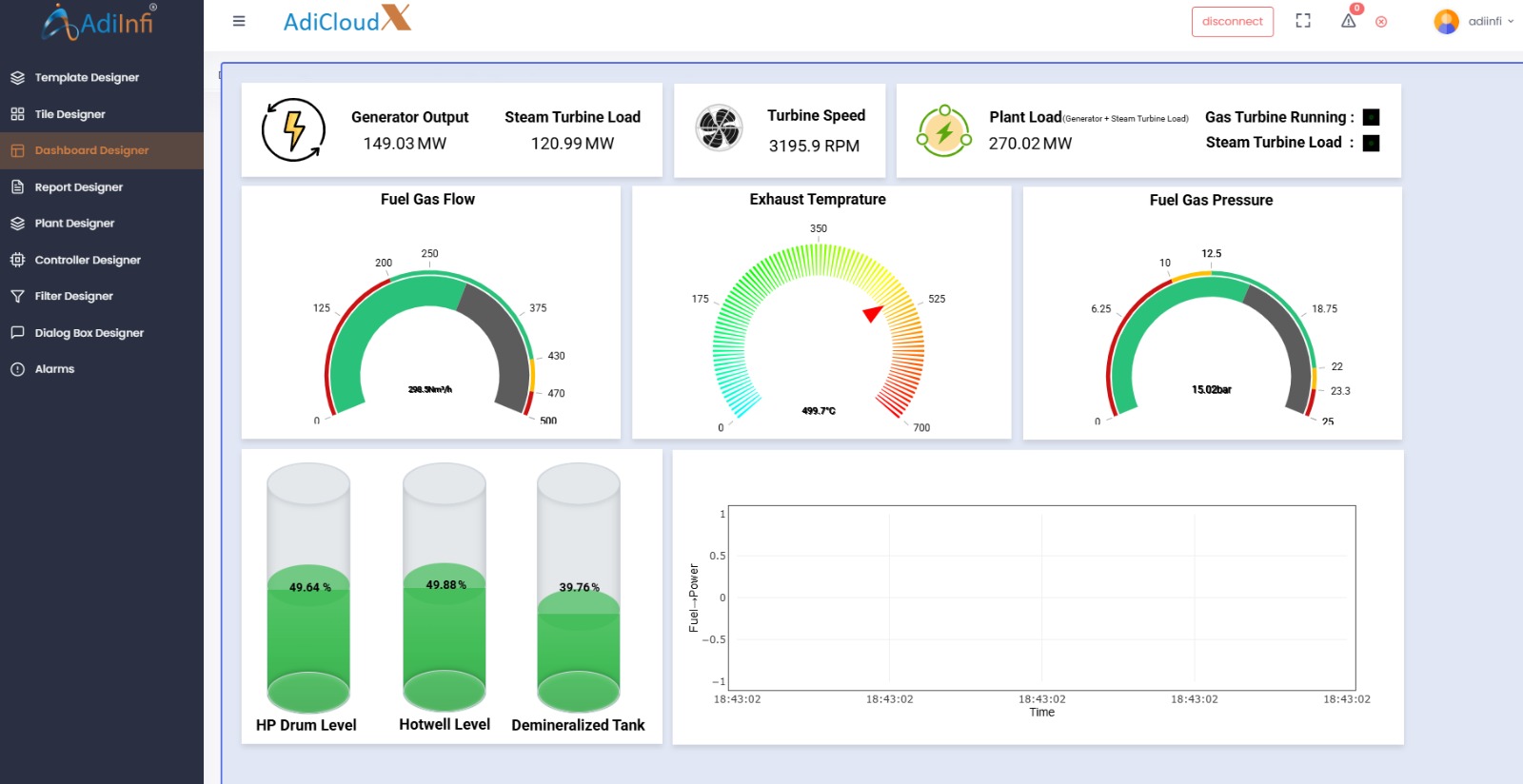
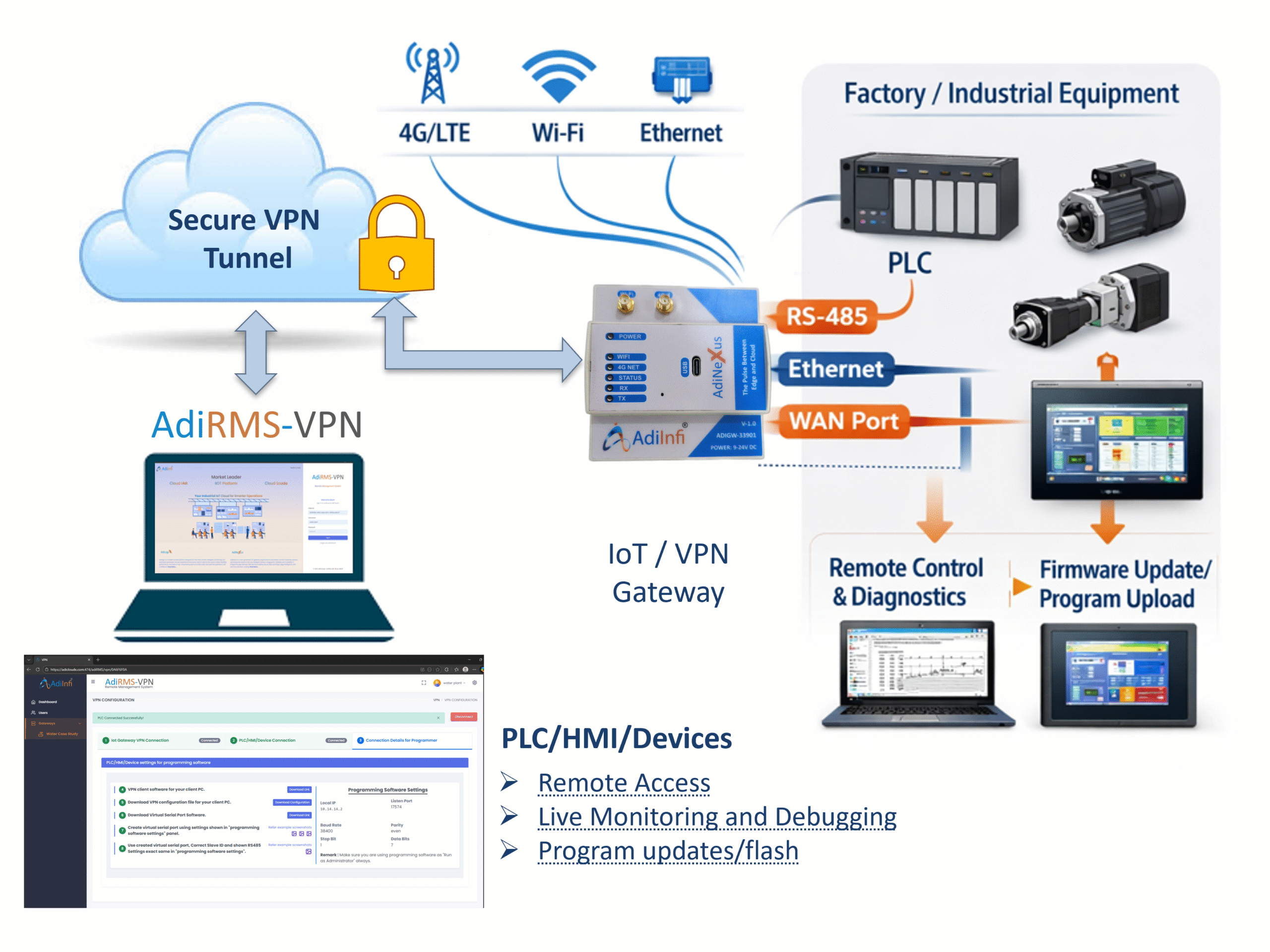
AdiLock is the all-in-one protection platform for .NET developers — combining military-grade code obfuscation with hardware-bound licensing, all from a single desktop application.
AdiLock – Build Log
09:41:02 ✓ Assembly loaded: MyApp.exe (1.2 MB)
09:41:03 ► Applying Symbol Renaming…
09:41:04 ✓ Renamed 847 symbols → a,b,c…
09:41:05 ► String Encryption (AES-256)…
09:41:06 ✓ Encrypted 312 string literals
09:41:07 ► Control Flow Guard active…
09:41:08 ✓ IL rewritten — 219 methods hardened
09:41:09 ✓ Anti-tamper checksum injected
09:41:10 ✓ completed
847
SYMBOLS HIDDEN
312
✓
Designed by Adiinfi. Built for developers
The Reality
Without protection, your compiled .NET code is only a Click away from being revealed.
Every .NET assembly you distribute can be decompiled in seconds with freely available tools. Without protection, your business logic, algorithms, API keys, and licensing logic are an open book — to your competitors, crackers, and pirates.
Reverse engineering in 30 seconds
Tools like ILSpy and dnSpy can reconstruct near-perfect C# source from any unprotected .NET binary.
License bypasses are trivial
Without hardware binding and cryptographic signing, a single patched byte is enough to crack your licensing check forever.
📦
One purchase, unlimited copies
Without machine-locked licenses, a single legitimate customer can share your software with thousands of users.
Revenue you'll never see
Every pirated copy is a paying customer lost. Protection isn’t optional — it’s how you protect the revenue you worked for.
What AdiLock Does
Two weapons.
One platform.
AdiLock combines deep code obfuscation with a full licensing engine — giving you everything you need to protect and monetize your .NET software.
Code Obfuscation Engine
String Encryption
Symbol Renaming
Control Flow Guard
IL Code Encryption
Anti-Debug
L1
L2
L3
L4
L5
L6
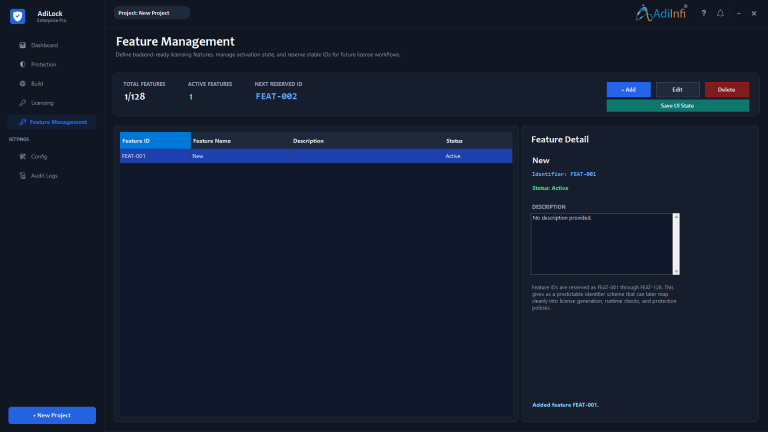
Licensing Engine
Digital Signing
Feature-Based Access
Hardware Binding
Tamper-Resistant
Permanent / Trial / Term
L1
L2
L3
L4
L5
L6
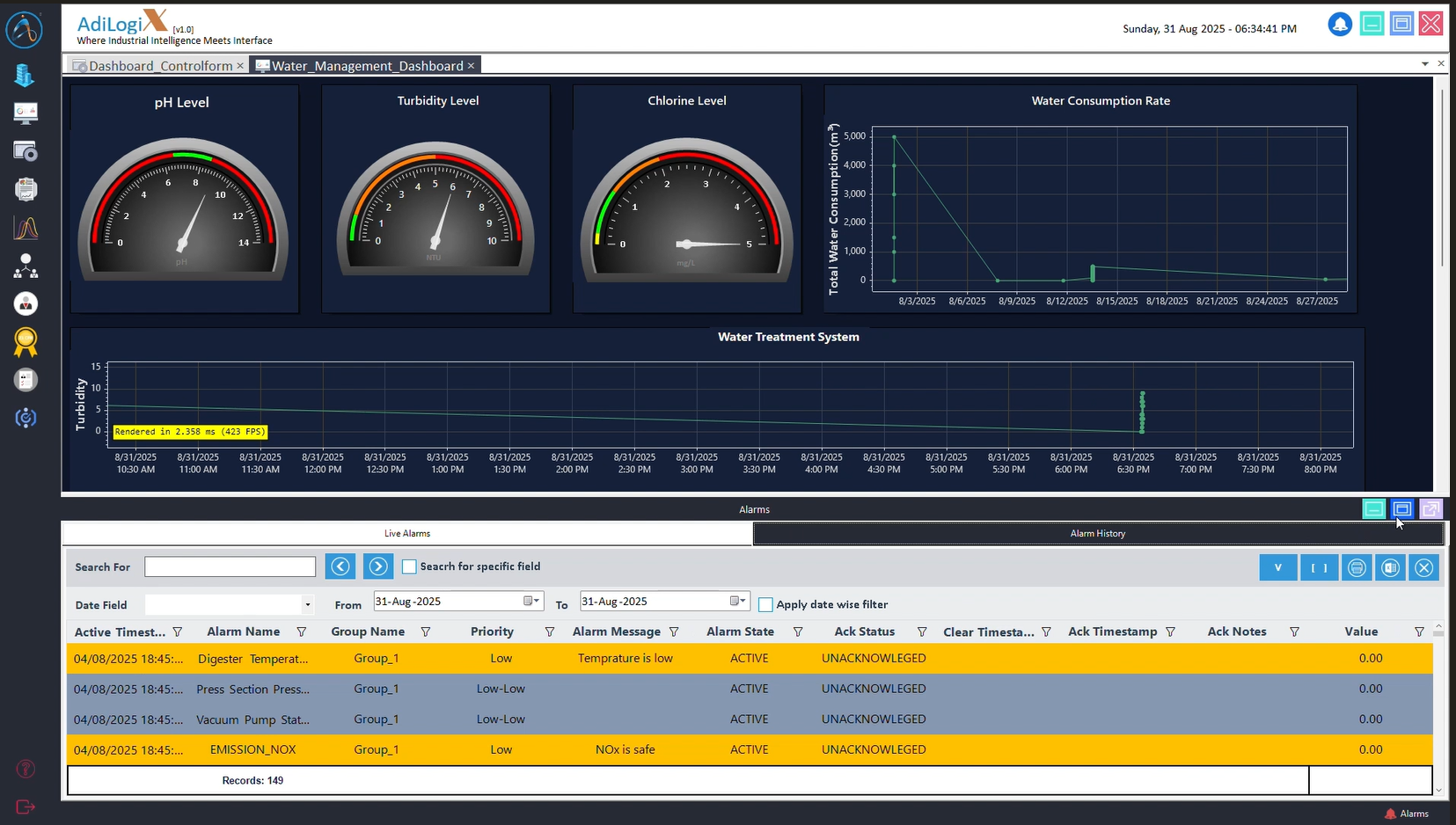
Hardware-Bound Licensing
Permanent
Trial
Term
Feature Licensing
128 feature slots
Stable IDs
Assembly Merger
ILRepack integration
Type collision handling
Runtime Email Notifications
Optional alerts
Run monitoring
Project Management
Reusable projects
Fast reload
IL Code Encryption
Runtime Decryption
Method-Level Protection
How It Works
Protection in four steps.
From compiled binary to hardened, licensed release — without touching a line of source code.
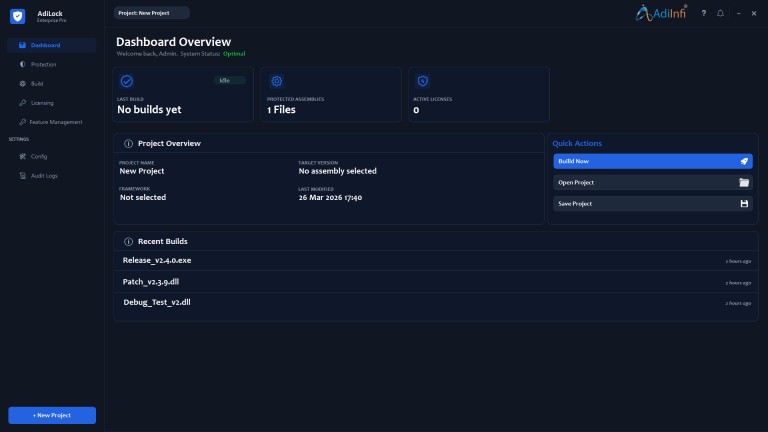
Open Your Project
Point AdiLock at your compiled .exe or .dll. The wizard loads the assembly and inspects every type, method, and field.
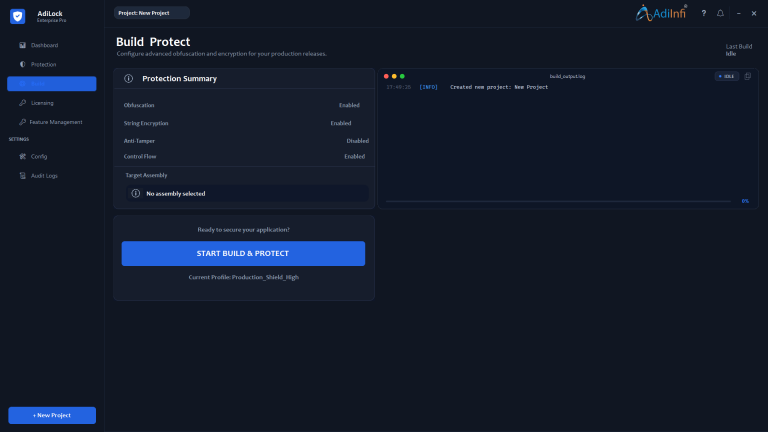
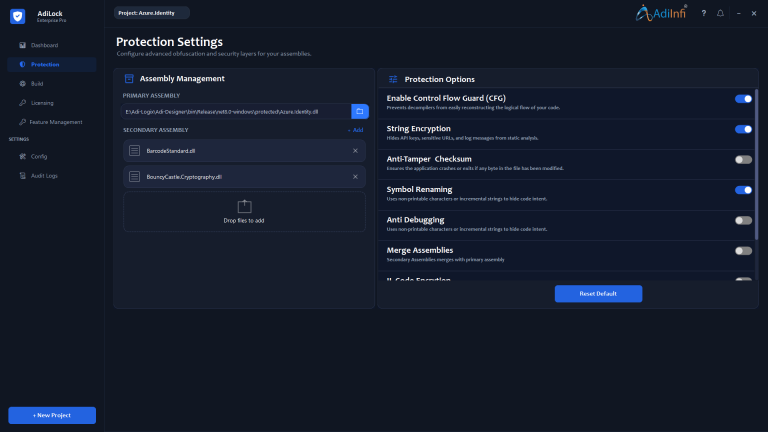
Configure Protection
Toggle the protection layers you need. Enable symbol renaming, string encryption, control flow hardening, and anti-tamper checks with a single switch each. Sane defaults, zero code required.
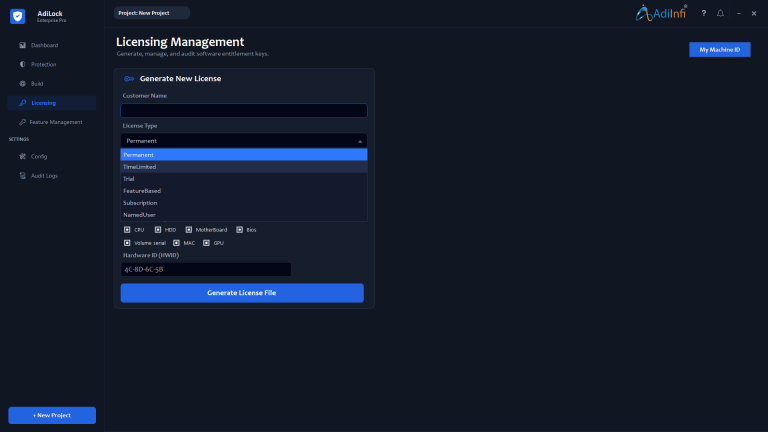
Generate Licenses
Enter your customer’s Hardware ID, choose a license type and expiry, select which feature flags they get. Click generate — AdiLock creates a cryptographically signed .lic file in seconds.
Build & Ship
Click Start Build. Watch the real-time log as AdiLock rewrites your IL, injects the license runtime, and produces the protected output. Ship the binary and the .lic file. Done.
Protection Layers
Every layer
matters.
Each protection option is independently togglable. Use the defaults for a strong commercial baseline — or stack every layer for maximum hardness against determined attackers.
Symbol Renaming
Every class name, method, field, and namespace becomes a, b, c… Removes all developer intent from the binary. Decompilers get meaningless variable soup.
String Encryption
Every hardcoded string — API keys, URLs, log messages, error text — is AES-256 encrypted at the IL level and decrypted only at runtime.
Control Flow Guard
Method bodies are converted to state-machine while-loops. ILSpy, dnSpy, and de4dot cannot reconstruct your logic from the resulting IL graph.
Anti-Tamper Checksum
Any byte protection modification kills the process instantly.
Anti-Debugging
Detects debugger attachment via multiple native APIs and timing analysis. Configure to exit silently, crash loudly, or continue undetected.
IL Code Encryption
Full method bodies are encrypted at the IL level and decrypted only at runtime by an injected stub. The strongest available protection — for your most critical code.
Pick your protection level.
Not every application needs every layer. AdiLock ships with sensible defaults for commercial releases, and lets you go further when the value demands it. The recommended combinations below are tuned for real-world threat profiles.
Standard
Maximum
Stealth
All options are independently togglable. Presets are one-click starting points — every project is different, and AdiLock gives you full control.
- CPU Processor ID
- BIOS Version
- MAC Address (physical)
- GPU Device ID
- Motherboard Serial
- HDD Serial
- Volume Serial
License Types
Every business model,
natively supported.
AdiLock generates signed, hardware-bound license files for all commercial models. One tool for your entire product catalog.
Permanent
Ties a customer to their machine forever. One-time purchase with no expiry. Ideal for perpetual-license software.
Trial
N-day countdown from first activation. Limits are enforced by an encrypted runtime check the customer cannot bypass.
Feature-Based
Assign specific feature flags per customer. Standard customers get FEAT-001; Professional customers get all 128 slots. One binary, infinite tiers.
Time-Limited Licensing
Generate licenses with a predefined validity period. Once the configured time expires, the license automatically becomes inactive. Perfect for trials, subscriptions, temporary deployments, or contract-based access control.
Why AdiLock
Designed by Adiinfi.
Built for developers.
AdiLock is developed by Adiinfi, leveraging 25+ years of .NET development experience. Built to eliminate complicated and costly licensing tools, AdiLock focuses on simplicity, flexibility, and reliable software protection.
No source code modifications required
Works on your compiled output. Your codebase and build process are untouched.
Project files save everything
.nsp project files preserve all settings and cryptographic keys. Reproducible builds every time.
IntelliLock feature parity, zero lock-in
Every major IntelliLock feature is matched — without the enterprise pricing or vendor dependency.
Layered architecture you can trust
Four-layer clean architecture. Domain engines fully independent of UI. xUnit test coverage throughout.
12+
128
7
0
Feature Comparison
AdiLock vs. the alternatives
Feature
Generic tools
AdiLock
Symbol renaming
✓
✓
String encryption
✓
✓
Control flow obfuscation
Partial
✓
IL Code Encryption
✓
✓
Hardware-bound licensing
x
✓
Digital-signed license files
x
✓
Feature-gated licensing (128 slots)
✓
✓
Assembly merger (single EXE)
Separate tool
✓
Anti-tamper + anti-debug
x
✓
Project files (.nsp) with key storage
x
✓
LOCK
Ready to lock down
your software?
AdiLock helps protect your .NET code and business model from reverse engineering, piracy, and tampering.
Built by AdiInfi · adiinfi.co.in · Secure. Lock. Protect.